[FIRMWARE] Itus Shield v2
1234
... 7

1234
... 7
|
Administrator
|
This post was updated on .
Below are the instruction for flashing the firmware on your Itus Networks Shield.
*** Disclaimer: I am not affliated, endorsed, or recognized by anyone who was associated with Itus Networks. This is a derived work of OpenWrt and released under GNU GPL 2.0. While I will always do my utmost to ensure the safety of the device, any liability risk of damage is yours, and yours alone. That being said, most of the Shield users probably aren't actually using it. Requirements: A working Itus Networks Shield, with at least the ability and knowledge of how to ssh/scp A USB console rollover cable would be ideal. (8N1 115200 8N1 Hardware/Software Flow Control OFF) If your shield isn't working at all, follow How to unbrick your Shield and get it at least working at that level, then come back. Background: The Shield was originally shipped with 3 modes and 4 eMMC partitions. Bridge, Router, Gateway modes available via front-position GPIO selector. This image will alter the Gateway mode, image, and partition. I used this slot because the original Shield Gateway image was reportedly non-functional anyway. This will NOT alter your BRIDGE/ROUTER images or settings. Flashing: Boot the Shield into any mode that you can access it via ssh/scp (Router mode, by default, is the easiest, and I am going to make the assumption it is being used) Download the ItusgatewayImage Now, we need to mount the storage partition on the Shield. On the device: umount /overlay
|
|
Administrator
|
Now that the Firmware is installed...
Packages: The Shield is a mips64 device on a CPU that isn't widely supported, but it doesn't mean it is BAD. However, it does mean we do not enjoy the same level of updates as everyone else. Currently, I am optimizing the build for Octeon3 devices, because that is what we have. I don't know the interoperability of the base mips64 packages OpenWrt does build (the core files are build-bot'ed). I'm still playing with it, but it's a software configuration rather than firmware. Until we figure it out, if you need/want/desire a OpenWrt package (official or not) built for the Shield, let me know and I will post the .ipk for it. Here is a listing of the Pre-Installed packages:
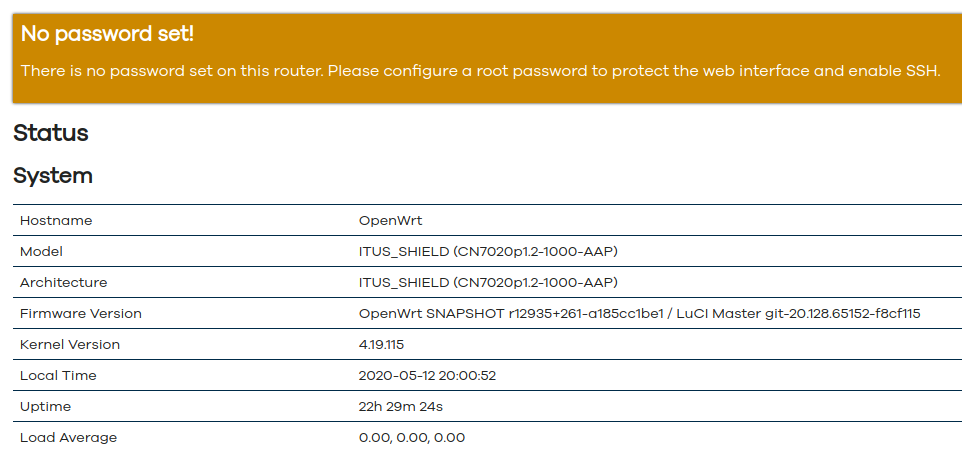
Running Itus Shield v2 Firmware
|
|
Administrator
|
Going Forward....
The Shield has tech specs that are higher-end consumer router devices. The Shield has a Dual-core 1Ghz CPU, just like my Netgear Nighthawk X6.. So, it probably will perform similarly, at least. Snort3 was my primary focus, since it is what the device was created for. It is loading a LOT of rules for testing. These might be trimmed down later. Anyone with LUA or Javascript experience who wants to work with me on creating a control interface for luCi, give me a shout.. Adblock is installed and enabled by default. General configurations are the best I know. If you have something better, test it and then share it with me.. I can bake it into future updates. Above all, have fun. I wouldn't think many people who didn't enjoy this sort of thing bought the Shield, so go have some fun with it.
Running Itus Shield v2 Firmware
|
|
Administrator
|
This is an updated init.d script for snort. Snort+ in inline-mode (-Q) screws with DHCP/DNS, so we'll remove it for now and reserve it for Bridge/Gateway mode.
Drop this file in /etc/init.d/snort: /etc/init.d/snort Then you can do a service snort restart
Running Itus Shield v2 Firmware
|
|
Got your email blast just now....
Cool! My Shield has been shelved since everything went belly up. I'll pull it out, power up and give this a try. Thanks for doing this. Wisi
Shield Pro v1, Chaos Calmer, FW 1.51 SP1, v8.3.2, Bridge Mode
|
|
Administrator
|
Welcome.. If you run into any issues, hit me up.
Running Itus Shield v2 Firmware
|
|
Wanted to come into the last thread for this, but see it's been closed.
I wanted to recommend a fan for the Shield. It works in consoles for modding the cooling (Dreamcast, specifically, I'm sure others), and it much quieter than stock, and cools better. |
|
Administrator
|
Good posting..
Cooling was a concern when I first started playing with the Shield. The temps never get excessive, but the "passive case cooling" model never gave me thrills.. I ended up trying to find a 5vDC fan that was actually 5vDC (and not 12vDC) so I could use the internal header, but never found one. I did throw a copper heatsink on there from a RaspPi and it seemed to help mitigate the heat You can see the post I made about it here. So, it's been a few days, whose gotten it to work and who is having issues?
Running Itus Shield v2 Firmware
|
|
Mine works, except I still need to do a reboot command after each boot (from cold) to get an IP but aside from that , brilliant! Thanks grommish
Running v2 Firmware
|
|
Administrator
|
I've not had that since getting the network driver reworked.. Hmm
Do me a favor and check your /etc/init.d/snort and see what the command string it. It should be procd_set_param command $PROG -v -c $config_dir/snort.lua -i $interface --daq-dir $daq_dir --daq $daq -l $log_dir -A $alert_module --create-pidfile -D
If you have the -Q in it, it'll act as a transparent bridge. But, again, I've not had those types of issues in a few builds. I'll test it here after I post this.. I'll power it off and let it sit, then bring it back up and see what happens.
Running Itus Shield v2 Firmware
|
|
Administrator
|
Actually.. In addition to checking the snort init.d, if you have shell access Turrican..
Grab this script (itus-custom-setup), put it on your Shield and run it.. This is the initial config script in the image, but deletes itself after first run. scp -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null itus-custom-setup root@10.10.10.10:/tmp
|
|
Administrator
|
Here is a video of the boot process from a cold, unplugged state..
https://youtu.be/XB-tjcb2Nio https://youtu.be/XB-tjcb2Nio
Running Itus Shield v2 Firmware
|
|
In reply to this post by Grommish
still the same Grommish, The script didnt help and the snort config is exactly the same as yours. From power on cold I must do a reboot command otherwise Eth0 does not get an ip. Totally consistent and repeatable.
Anyone else having this issue on the new V2 FW? or is it just me? strange as I have 2 shields and they both do this. Last thing I'm going to try later on is plugging the Shield DIRECTLY into my Cable Modem... see how that goes. I'll let you know Right now my set up is: Cable Modem -> Synology Router -> Switch -> Intra-house CAT6 cabling -> switch -> long cat6 cable ->switch ->shield Eth0 Sounds like a nightmare but everything always works on my workstation which is at the end of this chain also (desktop PC, work laptop, Synology NAS) but I'll cut all this connectivity out and connect to my modem just to test.
Running v2 Firmware
|
|
Administrator
|
My network is just as convoluted :)
I go Cable Modem -> Nighthawk X6 R8000. From the Nighthawk (192.168.1.0/24), I go to a 48-port switch off one port for the main network and a drop to a really old DLink DIR655 (192.168.5.0/24) that has a Server 2016 machine providing the DHCP/DNS/BOOTP. The Shield then comes off the DLink (10.10.10.0/24) and then goes to my laptop. Do me a favor.. On the Shield, unplug eth0 and then type: tcpdump -i eth0 -vvv -s 1500 '((port 67 or port 68) and (udp[8:1] = 0x1))' | tee /tmp/dhcplogThen plug eth0 back in. Give it a few seconds (or when it starts repeating), Cntl-c to stop it and then email me the /tmp/dhcplog file or post it. Also, can you also do: uci show > /tmp/configsand send that as well. This is what you SHOULD be seeing from the tcpdump tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 1500 bytes [151542.815599] eth0: Link down [151551.008458] eth0: 1000 Mbps Full duplex, port 0, queue 0 18:39:48.881198 IP (tos 0x0, ttl 64, id 0, offset 0, flags [none], proto UDP (17), length 328) 0.nextyourcontent.com.68 > 255.255.255.255.67: [udp sum ok] BOOTP/DHCP, Request from 2c:26:5f:00:00:00 (oui Unknown), lengt) Client-Ethernet-Address 2c:26:5f:00:00:00 (oui Unknown) Vendor-rfc1048 Extensions Magic Cookie 0x63825363 DHCP-Message Option 53, length 1: Discover MSZ Option 57, length 2: 576 Parameter-Request Option 55, length 8: Subnet-Mask, Default-Gateway, Domain-Name-Server, Hostname Domain-Name, BR, NTP, Classless-Static-Route Vendor-Class Option 60, length 12: "udhcp 1.31.1" Hostname Option 12, length 6: "Shield" END Option 255, length 0 PAD Option 0, length 0, occurs 20 18:39:48.897050 IP (tos 0x0, ttl 64, id 0, offset 0, flags [none], proto UDP (17), length 328) 0.nextyourcontent.com.68 > 255.255.255.255.67: [udp sum ok] BOOTP/DHCP, Request from 2c:26:5f:00:00:00 (oui Unknown), lengt) Client-Ethernet-Address 2c:26:5f:00:00:00 (oui Unknown) Vendor-rfc1048 Extensions Magic Cookie 0x63825363 DHCP-Message Option 53, length 1: Request Requested-IP Option 50, length 4: 192.168.5.110 Server-ID Option 54, length 4: 192.168.5.2 MSZ Option 57, length 2: 576 Parameter-Request Option 55, length 8: Subnet-Mask, Default-Gateway, Domain-Name-Server, Hostname Domain-Name, BR, NTP, Classless-Static-Route Vendor-Class Option 60, length 12: "udhcp 1.31.1" Hostname Option 12, length 6: "Shield" END Option 255, length 0 PAD Option 0, length 0, occurs 8
Running Itus Shield v2 Firmware
|
|
Will do when I get a chance
Cheers
From: Grommish [via Itus Networks Owners Forum] <ml+[hidden email]>
Sent: Tuesday, May 19, 2020 7:54:02 PM To: Turrican <[hidden email]> Subject: Re: Update to /etc/init.d/snort My network is just as convoluted :)
I go Cable Modem -> Nighthawk X6 R8000. From the Nighthawk (192.168.1.0/24), I go to a 48-port switch off one port for the main network and a drop to a really old DLink DIR655 (192.168.5.0/24) that has a Server 2016 machine providing the DHCP/DNS/BOOTP. The Shield then comes off the DLink (10.10.10.0/24) and then goes to my laptop. Do me a favor.. On the Shield, unplug eth0 and then type: tcpdump -i eth0 -vvv -s 1500 '((port 67 or port 68) and (udp[8:1] = 0x1))' | tee /tmp/dhcplogThen plug eth0 back in. Give it a few seconds (or when it starts repeating), Cntl-c to stop it and then email me the /tmp/dhcplog file or post it. Also, can you also do: uci show > /tmp/configsand send that as well. This is what you SHOULD be seeing from the tcpdump tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 1500 bytes [151542.815599] eth0: Link down [151551.008458] eth0: 1000 Mbps Full duplex, port 0, queue 0 18:39:48.881198 IP (tos 0x0, ttl 64, id 0, offset 0, flags [none], proto UDP (17), length 328) 0.nextyourcontent.com.68 > 255.255.255.255.67: [udp sum ok] BOOTP/DHCP, Request from 2c:26:5f:00:00:00 (oui Unknown), lengt) Client-Ethernet-Address 2c:26:5f:00:00:00 (oui Unknown) Vendor-rfc1048 Extensions Magic Cookie 0x63825363 DHCP-Message Option 53, length 1: Discover MSZ Option 57, length 2: 576 Parameter-Request Option 55, length 8: Subnet-Mask, Default-Gateway, Domain-Name-Server, Hostname Domain-Name, BR, NTP, Classless-Static-Route Vendor-Class Option 60, length 12: "udhcp 1.31.1" Hostname Option 12, length 6: "Shield" END Option 255, length 0 PAD Option 0, length 0, occurs 20 18:39:48.897050 IP (tos 0x0, ttl 64, id 0, offset 0, flags [none], proto UDP (17), length 328) 0.nextyourcontent.com.68 > 255.255.255.255.67: [udp sum ok] BOOTP/DHCP, Request from 2c:26:5f:00:00:00 (oui Unknown), lengt) Client-Ethernet-Address 2c:26:5f:00:00:00 (oui Unknown) Vendor-rfc1048 Extensions Magic Cookie 0x63825363 DHCP-Message Option 53, length 1: Request Requested-IP Option 50, length 4: 192.168.5.110 Server-ID Option 54, length 4: 192.168.5.2 MSZ Option 57, length 2: 576 Parameter-Request Option 55, length 8: Subnet-Mask, Default-Gateway, Domain-Name-Server, Hostname Domain-Name, BR, NTP, Classless-Static-Route Vendor-Class Option 60, length 12: "udhcp 1.31.1" Hostname Option 12, length 6: "Shield" END Option 255, length 0 PAD Option 0, length 0, occurs 8
Running Itus Shield v2 Firmware
If you reply to this email, your message will be added to the discussion below:
http://itus.accessinnov.com/FIRMWARE-Itus-Shield-v2-tp2014p2028.html
To start a new topic under Technical Discussion, email ml+[hidden email]
To unsubscribe from Itus Networks Owners Forum, click here. NAML
Running v2 Firmware
|
|
Administrator
|
Massive thanks to @Turrican for putting up with me during this testing! :D
Has anyone else experienced possible heat-related issues regarding the Shield? Turrican's shield refused to pull an IP address for no apparent reason - in fact, it was almost like the Network controller was simply not working at all. We worked on it for a bit before he had to go, and nothing.. After we gave up, I asked him to unplug it while he did what he had to do and revisit it once it cooled down (I had suspicions of thermal issues from almost day 1 with the Shield). He came back and it fired right up without issues.. My personal box has lived without the lid or "thermal pad" since the first week until yesterday, but even then, I have the copper block on the CPU (swapped for the foam pad) and it's under an AC vent. So, if during testing you seem to have network issues, try letting it sit for 5-10 minutes and trying again.. If it works, maybe we can figure out how to mediate the thermals most effectively.
Running Itus Shield v2 Firmware
|
|
Administrator
|
How to deal with heat?
I've added the collectd subsystem to the latest image to see what sensor data we can collect. Thermals doesn't seem to be working and the sensor package is completely erroring out. I've got a post up on OpenWrt to see if it can be fixed or what I missed. In the mean time? It's what I had laying around, but it'll certainly show if heat-soak is an issue... 
Running Itus Shield v2 Firmware
|
|
Bought the exact fan which ltleg recommended (thanks for that) but I can’t get it working. I plugged it into what I assumed was the fan header (white socket on left under reset switch pictured below) but it doesn’t move. Not sure if it’s maybe thermally controlled? Any ideas? Thanks
61228BFD-EFC8-497A-823F-37CF77A2FE0D.jpeg
Running v2 Firmware
|
Re: Potential thermal issues on Shield
|
Hi I have a Nvidia Jetson nano and I bought the except same fan as you, placed it on the 3 pins on the white socket and nothing happened I found out later that you have to run a script to set the fan speed this link below it's what I use on the nano and works fine, but it needs python, not sure is the Shield has got python installed by default Roadrunneruk On Mon, 25 May 2020 at 12:27, Turrican [via Itus Networks Owners Forum] <[hidden email]> wrote: Bought the exact fan which ltleg recommended (thanks for that) but I can’t get it working. I plugged it into what I assumed was the fan header (white socket on left under reset switch pictured below) but it doesn’t move. Not sure if it’s maybe thermally controlled? Any ideas? Thanks |
|
Administrator
|
I could never get that fan header to do anything. I went thru 3 fans I bought and nothing. I'll look at that script, Road! I don't know if I put python 3 back in or not. It usually isn't in OpenWrt because of its size. We don't have that issue, so I built it in at one point. Thanks for all the help all! On Mon, May 25, 2020, 10:05 AM Roadrunnere42 [via Itus Networks Owners Forum] <[hidden email]> wrote:
Running Itus Shield v2 Firmware
|
«
Return to Technical Discussion
|
1 view|%1 views
| Free forum by Nabble | Edit this page |